Symptoms: USB Device Detection Issues
When attempting to access data on an external USB hard drive, you may encounter the following error message:
“USB Device not recognized: One of the devices attached to this computer has malfunctioned, and Windows does not recognize it.”
Applies to: Windows 10, version 1709, Windows 7 Service Pack 1 Original KB number: 2654149
Cause: Several situations can lead to the “USB Device not recognized” error:
The currently loaded USB driver has become unstable or corrupt.
Your PC requires an update for issues that may conflict with a USB external hard drive and Windows.
Windows may be missing other important updates for hardware or software issues.
Your USB controllers may have become unstable or corrupt.
Your external drive may be entering selective suspend.
Your PC motherboard may need updated drivers.

Resolution 1 – Uninstall and then reconnect the external hard drive:
This method addresses issues where the currently loaded USB driver has become unstable or corrupt.
Select Start, type Device Manager in the Search box, and then choose Device Manager from the returned list.
Under Disk Drives, find and press and hold (or right-click) the USB external hard drive with the issue, then select Uninstall.
After the hard drive is uninstalled, unplug the USB cable.
Wait for 1 minute and then reconnect the USB cable. The driver should automatically load.
Check for the USB drive in Windows Explorer.
Note: Avoid connecting your USB external
hard drive into a non-powered
USB hub as it may lack enough power to operate the external drive. Instead, plug it directly into your computer.
If this method does not resolve the issue, proceed to resolution 2.
Install hotfixes that resolve issues on Windows 7:
These hotfixes can address known conflicts between a USB external hard drive and Windows.
Go to KB976972 titled “You encounter problems when you move data over USB from a Windows 7-based computer that has an NVIDIA USB EHCI chipset and at least 4 GB of RAM.”
Under Update information, select the appropriate download link that corresponds to your version of Windows 7 (32-bit or 64-bit).
Follow the onscreen instructions to complete the download and installation.
Additionally, visit KB974476 titled “The computer stops responding when a USB device resumes from the USB Selective Suspend state in Windows 7,” and request and install the hotfix for your version of Windows 7.
Restart your computer after installing the hotfixes.
If your problem still persists, proceed to .
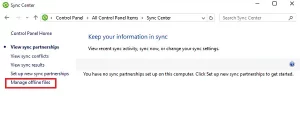
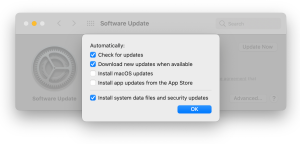
Install the latest Windows Updates: This method involves installing the latest device drivers for your USB external hard drive.
Select the Start button, type Windows Update in the Search box, and then choose Windows Update in the results pane.
Select Check for Updates. After the scan is complete, select Review optional updates.
Select the check box next to the updates and then choose Install updates.
Follow the onscreen instructions to download and install the updates.
If prompted, reboot your computer.
If your problem persists, proceed to resolution 4.
Reinstall USB controllers: This method addresses situations where the currently loaded USB driver has become unstable or corrupted.
Select Start, then type Device Manager in the Search box, and then choose Device Manager.
Expand Universal Serial Bus controllers. Press and hold (or right-click) each USB device and select Uninstall. Repeat for each device.
Once complete, restart your computer. Your USB controllers will automatically reinstall.
If your problem still exists, proceed to resolution 5.
Resolution 5 – Disable USB selective suspend setting: This method prevents your USB external drive from powering down.
Select the Start button, type power plan in the Search box, and then choose Choose a power plan.
Next to your currently selected plan, select Change Plan Settings.
Select Change advanced power settings.
Expand USB Settings > USB selective suspend settings.
Select Plugged in, choose the drop-down menu, and then select Disabled.
If you’re using a laptop, select Battery, choose the drop-down menu, and then select Disabled.
Select Apply > OK.
If this doesn’t resolve your issue, proceed to.
Install your motherboard’s latest chipset drivers: This method involves updating your motherboard’s chipset drivers so your computer will recognize your USB external hard drive.
Review your computer’s documentation to find the name of the motherboard manufacturer.
Visit your computer manufacturer’s support website and navigate to find the appropriate drivers for your motherboard.
Download and install the latest chipset drivers following the manufacturer’s instructions.
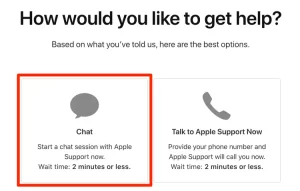
If your issue still persists, we recommend contacting Microsoft product support for further assistance.
By following these troubleshooting steps, you can resolve USB device detection issues in Windows and regain access to your USB external hard drive. Remember to check each resolution method carefully, and if one doesn’t work, proceed to the next until the issue is resolved.