Introduction to Beta Testing
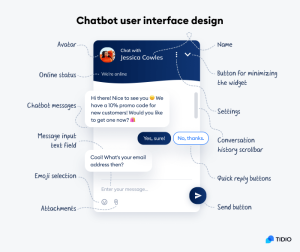
Beta testing is a pivotal phase in the software development life cycle, where a software product or service is tested in a real– world terrain before its sanctioned release. During beta testing, named druggies, frequently appertained to as beta testers, are given access to the software to use it in colorful scripts and give feedback on their experience. This feedback is inestimable to inventors as it helps identify bugs, glitches, and usability issues that may have been overlooked during the development process.
The Need for Beta Testing
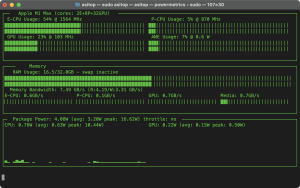
Beta testing is necessary for several reasons. It helps identify and fix bugs, ensures software quality, evaluates performance, gets stoner feedback, and improve stoner engagement. By involving real druggies in the testing process, inventors can gain perceptivity into how the software performs in real– world scripts, leading to an enhanced stoner experience and increased client satisfaction.
Characteristics of Beta Testing
Beta testing is performed by guests or druggies who aren’t workers of the company. It generally uses black– box testing and is carried out in the stoner‘s position without the need for a lab or testing terrain. trust ability, security, and robustness are checked during beta testing.

Types of Beta Testing
There are colorful types of beta testing, including Traditional Beta Testing
- Public Beta Testing
- Technical Beta Testing
- Focused Beta Testing
- Post-release Beta Testing
Criteria for Beta Testing
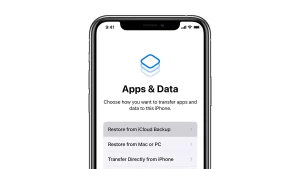
For beta testing to be effective, certain criteria need to be met. These include subscribing off a document on nascence testing, having the beta interpretation of the software ready, and icing an terrain ready for public release.
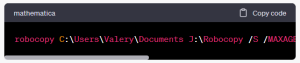
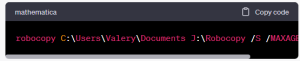
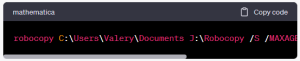
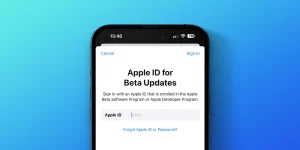
Tools Used for Beta Testing
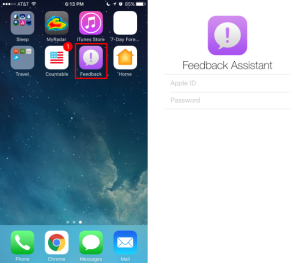
Several tools are available for beta testing, similar as Test Fairy, Center Code, Try My UI, User Testing, Test Rail, User snap, Zephyr, and Test Flight. These tools help streamline the beta testing process and gather precious feedback from beta testers.
Uses of Beta Testing
Beta testing serves multiple purposes, including relating and fixing bugs, testing software comity, gathering stoner feedback, assessing performance, and erecting client fidelity. It involves druggies in the development process, making them feel valued and engaged.
Advantages of Beta Testing
Beta testing offers several advantages, similar as reducing product failure threat through client confirmation, perfecting product quality through client feed back, being cost–effective compared to other data gathering styles, creating goodwill with guests, and adding client satisfaction.
Disadvantages of Beta Testing
Despite its benefits, beta testing has some downsides, including implicit complexity in tracking crimes due to varying testing surroundings, the possibility of indistinguishable bug reports, lack of control over the real– time testing terrain, and time– consuming feedback collection.
Conclusion
Beta testing plays a vital part in the software development process, helping identify bugs, ameliorate software quality, and gather stoner feedback. It’s an essential step toward icing a successful product launch and structure strong client connections. By engaging real druggies in the testing process, inventors can enhance the software’s overall performance and give druggies with a high– quality, dependable product.