This comprehensive guide is designed for Windows 11 users who are seeking ways to optimize their system’s performance by disabling Microsoft Edge’s tab preloading feature. The audience comprises individuals who have a basic understanding of Windows operating systems and are familiar with concepts like system settings, registry editing, and third-party applications.
Introduction: Disable Microsoft Edge Tab
In the realm of Windows 11, Microsoft Edge stands as the default browser, steadfastly integrated into the operating system. However, not all users find themselves enamored by its offerings, often preferring alternatives that align more with their browsing habits. One peculiar characteristic of Microsoft Edge is its “tab preloading” feature, which, while serving Edge aficionados, can be a resource-draining nuisance for those who have chosen a different path. This article delves into the world of tab preloading and presents four distinct ways to disable it in Windows 11, offering users the power to optimize their computing experience and conserve valuable system resources.
Understanding Microsoft Edge Tab Preloading
Before we embark on our journey to disable tab preloading, let’s fathom what it entails. Tab preloading is the practice of loading the Start and New Tab pages of Microsoft Edge while signing in to your Windows 11 PC. Although a boon for Edge enthusiasts, it might amount to a superfluous drain on system resources for users who’ve opted for other browsing alternatives. The next sections elucidate methods to tame this resource-consuming behavior.
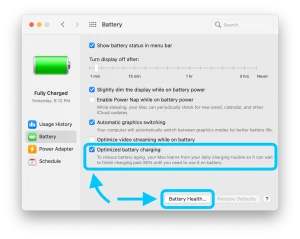
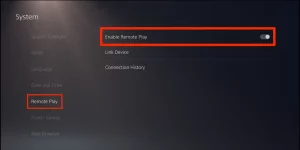
Using the Group Policy Editor to Disable Tab Preloading
For those traversing the Windows 11 landscape in Pro, Education, or Enterprise realms, the Group Policy Editor is a tool of considerable might. It bestows the ability to configure system policies and personalize the computing environment. If you’re among the fortunate wielders of this editor, the path to disabling tab preloading is relatively straightforward:
- Initiate a search by pressing Win + S and typing “gpedit.msc” into the text box.
- In the Group Policy Editor, navigate through User Configuration > Administrative Templates > Windows Components > Microsoft Edge.
- Locate the policy “Allow Microsoft Edge to start and load the Start and New Tab page at Windows startup and each time Microsoft Edge is closed.” Disable it by modifying the options.
- Apply the changes and restart your PC to witness the newfound optimization.
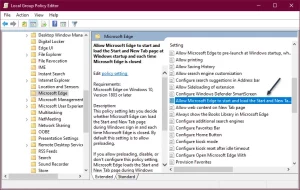
Image by:https://techsavvy.life/
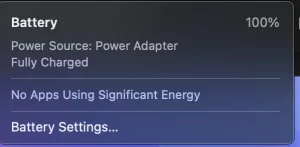
Registry Editor Method for Home Users
For those dwelling in the Home iteration of Windows 11, the path to tab preloading eradication takes a different route. The Registry Editor assumes the role of protagonist, offering a manual means of disabling this behavior:
- Prioritize safety by backing up your registry.
- Open the Run dialog by pressing Win + R and entering “regedit.”
- Navigating through HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\MicrosoftEdge\Main, create a new DWORD (32-bit) Value named “AllowPrelaunch” and set its value data to 0.
- Forge a new path through HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\MicrosoftEdge and create a new key named “TabPreloader.”
- Within this key, create another DWORD (32-bit) Value named “AllowTabPreloading” and set its value data to 0.
- After applying these changes, restart your PC to bask in the realm of preloading-free browsing.
Image by:https://winaero.com/
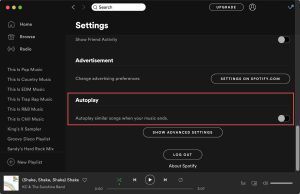
Streamlining the Process with Third-Party Apps
For those seeking a simpler solution, a third-party champion steps onto the stage: the Ultimate Windows Tweaker app. This app offers a user-friendly approach to disabling tab preloading:
- Begin by acquiring the Ultimate Windows Tweaker app and installing it on your PC.
- Launch the app, employing administrative privileges.
- Employ the “Search For Tweaks” option and query “edge tab.”
- Enable the “Disable Edge Tab Preloading” option and execute the tweaks.
- Bid adieu to tab preloading, and after closing the app, embark on a system restart.

Image by:https://www.reflectiz.com/
Making the Right Choice for You
In this expedition, we’ve explored multiple paths to vanquish tab preloading from Windows 11. Whether you wield the power of the Group Policy Editor, take the registry route, or harness the convenience of a third-party application, the result remains the same—a resource-optimized computing experience tailored to your preferences. The choice is yours, the tools are at your disposal; now, enhance your Windows 11 voyage by disabling Microsoft Edge’s tab preloading and embracing a smoother, more efficient journey.
Conclusion
In the realm of Windows 11 customization, the ability to disable Microsoft Edge’s tab preloading unveils a world of optimization. No longer shall you endure the resource drain imposed by tab preloading if you opt for other browsers. With the Group Policy Editor, the Registry Editor, or the Ultimate Windows Tweaker app, you’re empowered to shape your computing experience. By following the paths outlined in this guide, you’ll liberate your system resources, resulting in a more streamlined, efficient, and personalized Windows 11 journey. Say goodbye to unnecessary tab preloading and embark on a browsing experience that aligns seamlessly with your preferences.